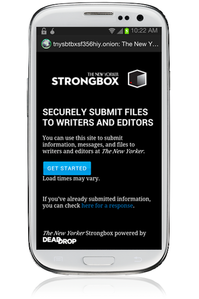
The Only Way to Visit Strongbox on a Phone
By mark · May 16, 2013
The New Yorker magazine just launched Strongbox, a whistleblower submission system that’s hosted on a hidden website. There’s only one way to access the hidden site on a phone or tablet, and that’s with our Orweb app. Here’s a simple breakdown of how to do securely and anonymously blow the whistle, explained in an interactive tutorial:
Visit guardianproject.info/howto/strongbox for an interactive tutorial on using Strongbox on your phone.
The website exists as a hidden site on what is widely known as the darknet, since you are going there hidden or “in the dark.” Instead of a .com, .org, or .info address (like guardianproject.info) the sites like Strongbox show up with a .onion. And like you need a web browser to go to a .com web address, you need a darknet browser to go to a .onion darknet address. On a mobile, we make the most secure and anonymous darknet & web browser, Orweb. And if you want to get to strongbox on your phone, we’re the only way to do it.
To browse, you’ll need our Orweb app. It’s currently only available for Android and you can get it here. If you have another type of phone or tablet, unfortunately you’ll have to use a computer.
For Orweb to be anonymous and give you access to the darknet .onion addresses, you’ll need to enable onion routing with our Orbot plugin. This plugin gives Orweb and other compatible apps (like our Gibberbot secure chat for Facebook, Google, & Jabber) the ability to send web traffic through the darknet, thus avoiding tracking as well as blocking. You can download Orbot here. It’s the official app of the Tor Project, which develops the onion routing protocol, on Android.
Once both are installed, you just need to go to this hidden site: http://tnysbtbxsf356hiy.onion . Make sure that you’re using the Orweb browser and that Orbot is running. From there, you can easily submit messages to The New Yorker. Unfortunately you can’t yet submit files to them through the phone just yet.
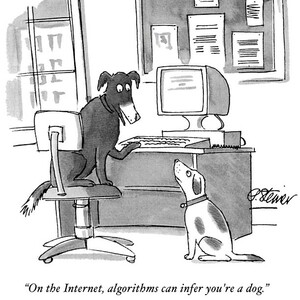
Overall, this is an exciting step in the right direction. With an increase in tracking and crackdown on political dissidents and whistleblowers around the world, there need to be safe and trusted ways of sharing information that has the potential of saving lives and making the world a better place. The New Yorker is one of the most trusted journalistic outfits in the world and it will be interesting to follow how they understand and vet information that comes in from anonymous sources. It will be a lesson for the entire privacy community.
At the same time, it’s not yet a trusted technology. While the code is accessible and open source it is unclear whether it’s a full version of the DeadDrop code that it came from or a fork of it. It also hasn’t been audited yet. Already, we’re seeing issues popping up on the code. Hopefully it will be fully vetted as a solution and stand up to the ambitious and crucial claims that it is able “to provide you with a greater degree of anonymity and security than afforded by conventional e-mail.”
In the months before January, I worked a few seats down from Aaron Swartz in the ThoughtWorks offices. Since those shocking days, it’s been inspiring to continue to see his legacy. I spoke with him a bunch of times about using technology to introduce truly disruptive techniques for empowering people whose rights were otherwise being trampled. At the time, we were working on Crowdring, an intiative from /The Rules. And we spoke about the power of leveraging telephony to give voice so widely, and the trade off of handing over personally identifiable information. He recognized the need for constantly evolving and shifting tactics and was expert at integrating that into both strategy and code. It’s an honor to continue to work with him now, and with the rest of the open source community as we all contribute code and ideas to make the world better.
Having just won the Knight News Challenge for our Informacam project, we’re excited at the growing interest from the world of journalism in making sure that sources are kept truly secure and anonymous in the digital age. We’re working to build our whole suite of tools to make it easier and better to do so. If you want to reach out to us, anonymously or otherwise, to let us know how we can help, you can use Orbot and Tor to do so over any of these methods. We look forward to it!