Security Awareness Party
By mark · April 26, 2013
In the security world, there’s a pesky belief that a tool can either be secure or easy to use, but not both. Some experts also argue that training people to be safe online is too hard and doesn’t accomplish much (see Bruce Schneier’s recent post Security Awareness Training). Without a thoughtful approach, that’s usually how it plays out. But it doesn’t have to be that way! We’re committed to making online security fun to learn and fun to use, and we’re launching a new series of interactive tutorials to make it happen. Consider this post an invitation to our festive Security Awareness Party. Beer is encouraged, especially if it comes from an Android-powered kegbot.
Here at Guardian, security is always our #1 priority. We owe that to our users who rely on us to keep them safe in places like Syria or Iran. But the time we spend on encryption is wasted if users don’t like using our tools, or can’t figure out how they work. We want to make security apps that are enjoyable and easy to use everyday, and don’t take a PHD to understand.
Activists in Iran and Syria know firsthand how important technologies like Tor and VPNs are for staying safe online. Our friends and neighbors might not be living under a repressive dictatorship, but that doesn’t mean they couldn’t use a little digital security in their lives. Maybe your nephew wants to get past the block on Facebook at school, or your co-worker wants to watch March Madness at work (make sure she gets that decoy spreadsheet ready). Maybe your friend just wants to send his wife a few…private messages, and he’d rather not have them stored by Google or Verizon. These people might not be pros, but they’re curious and happy to poke around their technology. With a little fun and interactive guidance, they can be well on their way to becoming a power user. Everyone starts somewhere!
We want to make life safer and easier for at-risk activists and everyday people alike. That’s why we make accessible and straightforward guides to help you quickly and easily get past censors, internet police, or the office IT department.
Gibberbot Tutorial
Our newest tutorial is for our secure chat app, Gibberbot. With your Android phone in one hand and the Gibberbot Tutorial in the other, you can be chatting securely on Google or Facebook chat in minutes! But Google and Facebook can’t even tell what you’re talking about. It’s also more convenient to have all of your chat apps rolled into one so that it doesn’t matter where your friends message you, it still goes to the same place. Gibberbot works even if someone is trying to monitor or block your phone’s communications. If you know another language and would like to contribute, we’d love your help translating the tutorial (we’ve got English and Tibetan covered).
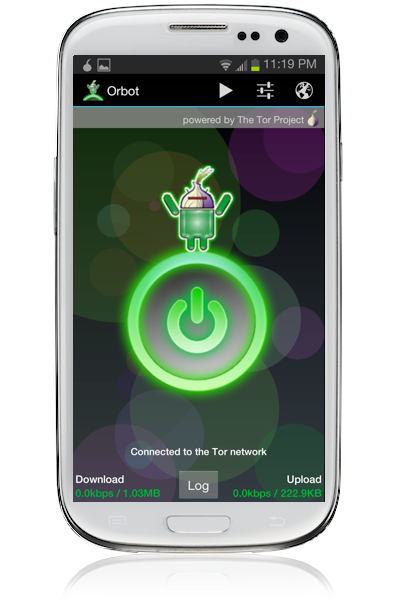
Orbot Tutorial
With our Android app Orbot, browsing the web securely and safely through Tor has been a piece of cake for a while now. But we just created an interactive tutorial to get you started and show how easy it is circumvent censorship, even if the Google Play Store is blocking direct access to our app.
The tools themselves are getting smarter too. A new tool from Tor, called Pluggable Transports, hides your Tor traffic to look like regular Internet traffic, making it even easier for Tor users to stay ahead of surveillance and censorship. To use this new tool with Orbot, just follow the instructions on our new one-page guide (and in Farsi) and you’re all set! For a more in-depth guide to using Orbot, watch our video tutorial (now in English and Arabic).
As we continue to grow our team and create new tools, we need your feedback! Please tell us what we can do to go from security awareness training to a full-on security awareness party. Feel free to leave a comment on this post or tell us how we can make things easier through our contact page. You can also let us know about any upcoming parties that we should be attending.
<p>
<i>This post is partially a response to Bruce Schneier’s recent piece: <a title="Schneier Security Awareness Training" href="https://www.schneier.com/blog/archives/2013/03/security_awaren_1.html">Security Awareness Training</a></i>.
</p>